A Guide to Claims-Based Identity and Access Control: Authentication and Authorization for Services and the Web: Authentication and Authorization for Services, Web, and the Cloud : Baier, Dominick, Bertocci, Vittorio, Brown, Keith,

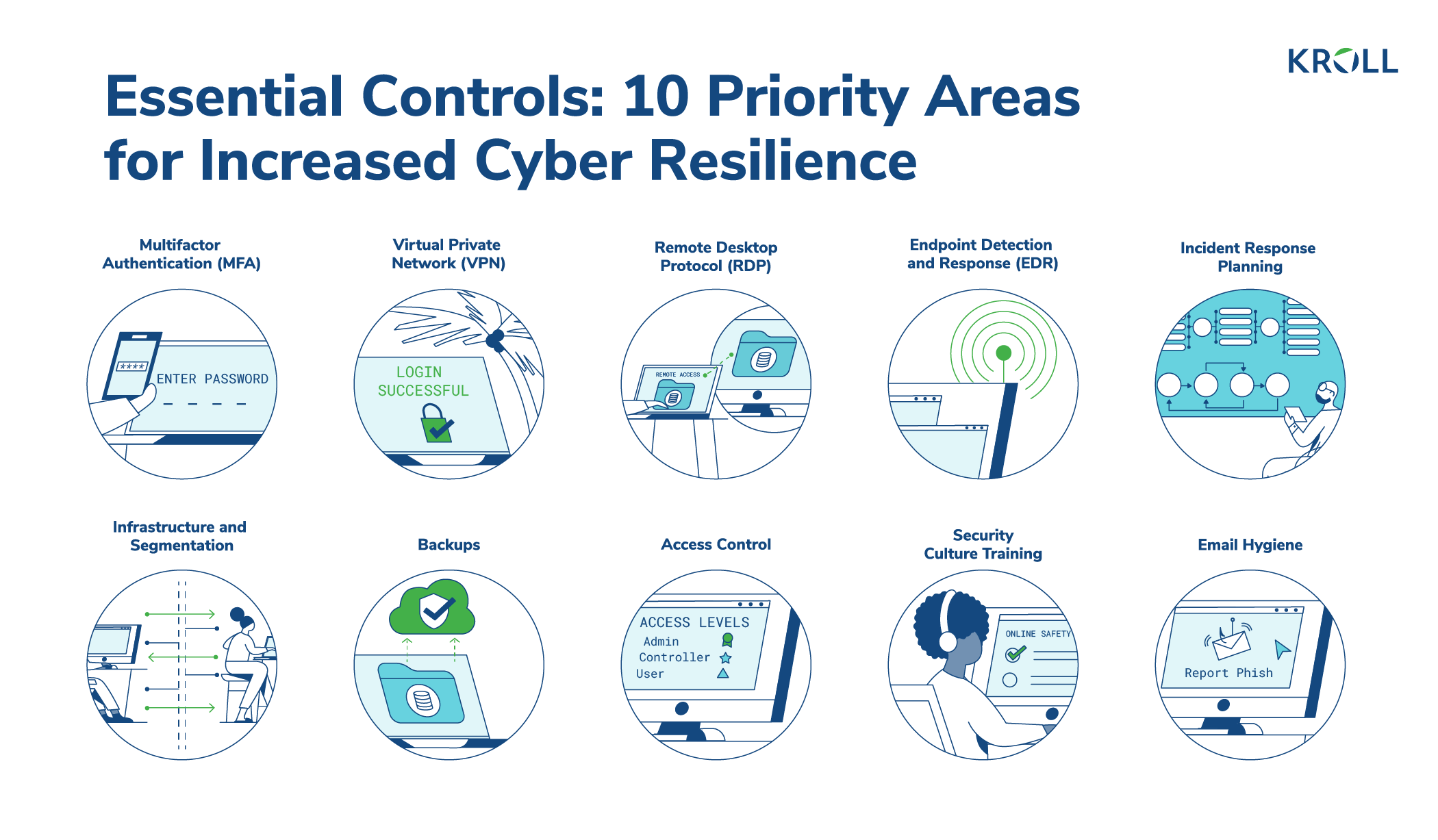
Free Course: Information Security - Authentication and Access Control from New York University (NYU) | Class Central
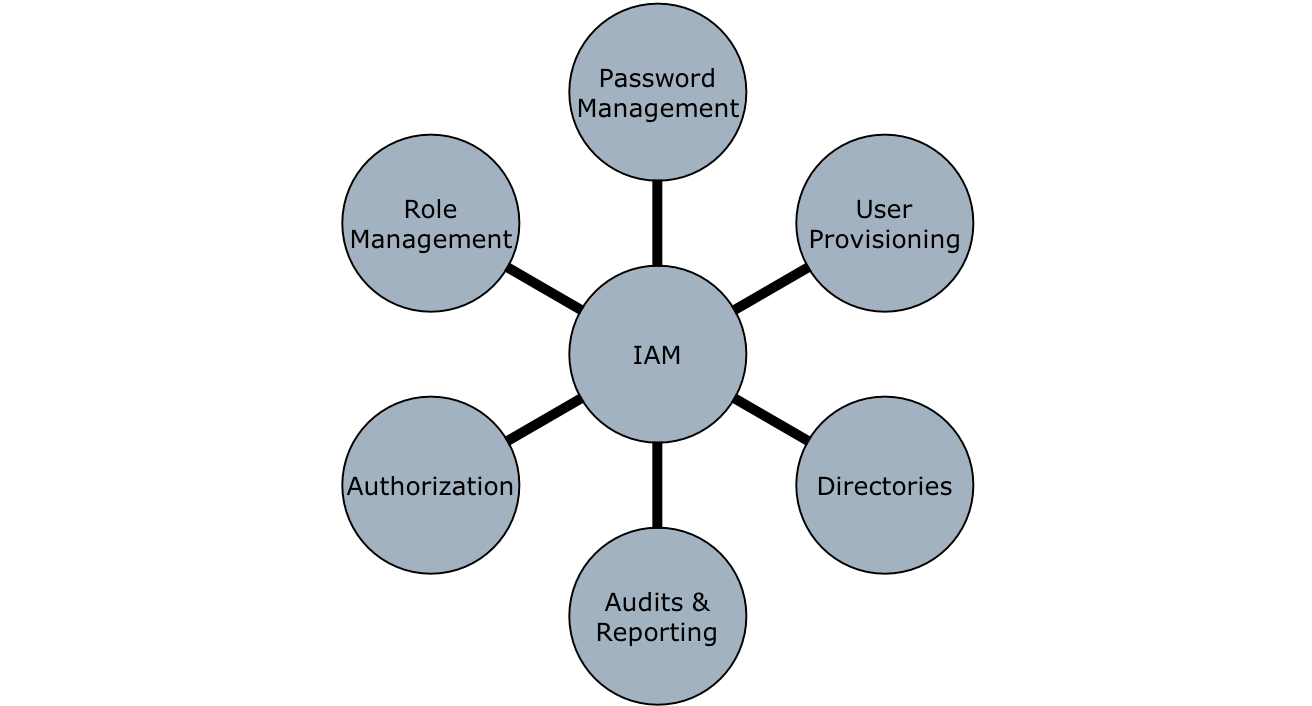
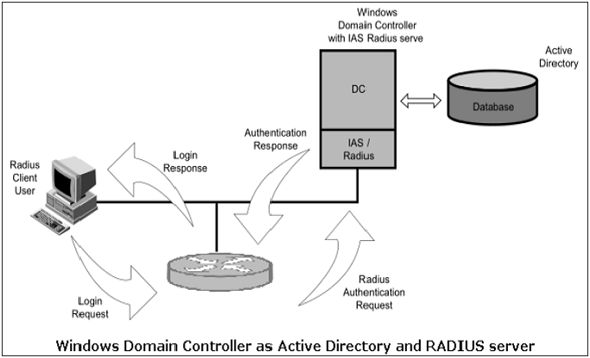
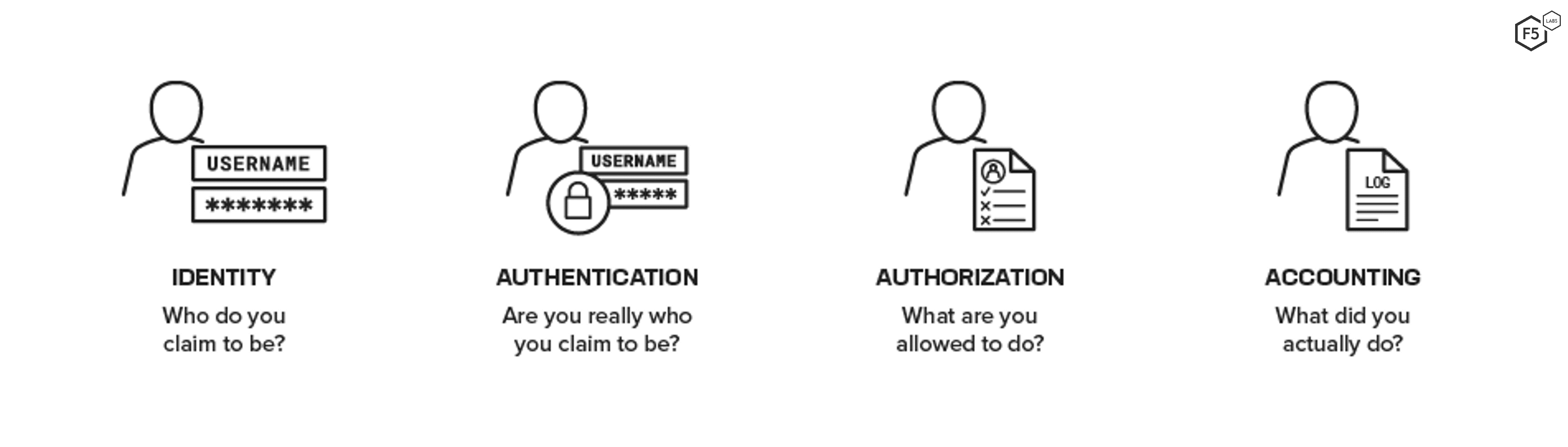
3 Basic A's of Identity and Access Management -Authentication, Authorization, and Accounting – Xorlogics

Authentication and Access Control - Boonkrong, Sirapat - Ebook in inglese - EPUB3 con Adobe DRM | IBS

A Guide to Claims-Based Identity and Access Control: Authentication and Authorization for Services and the Web : Baier, Dominick, Bertocci, Vittorio, Brown, Keith, Densmore, Scott, Pace, Eugenio, Woloski, Matias: Amazon.it: Libri